
How to perform a cyber security risk assessment
Read more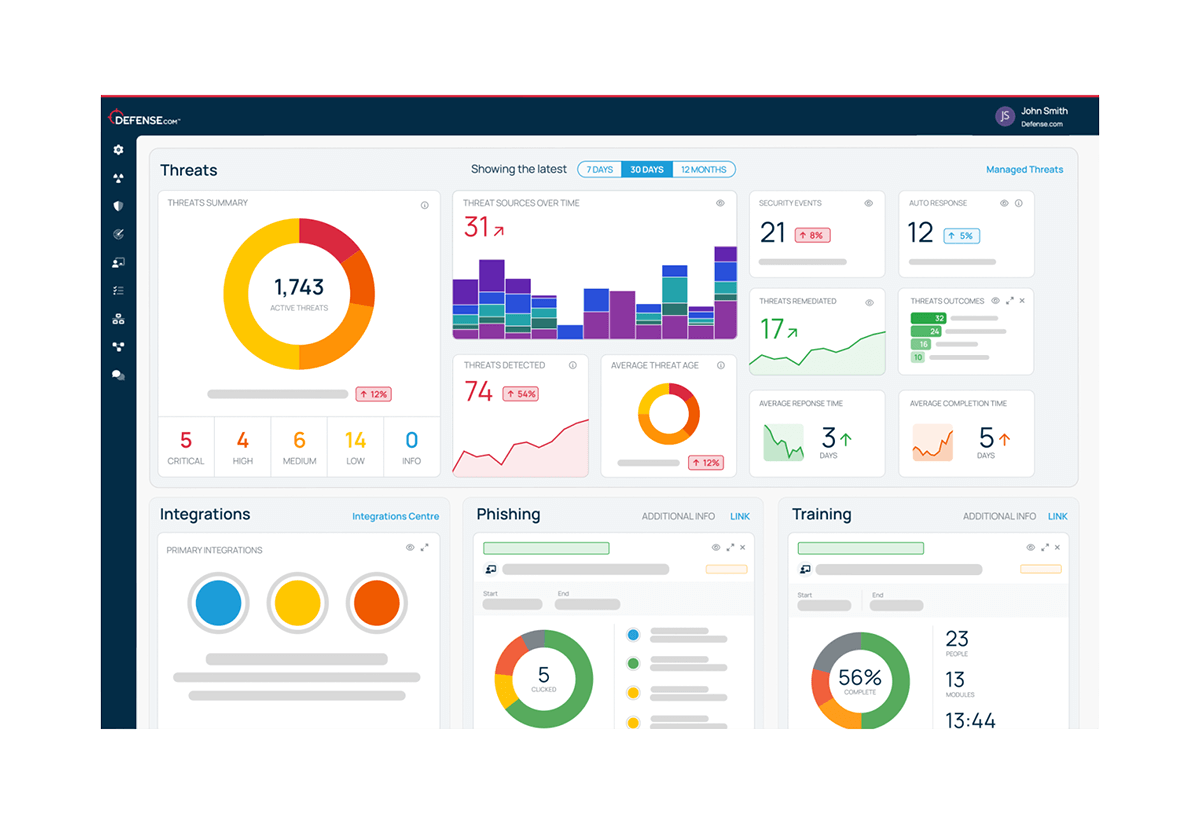
Defense.com eXtended Detection & Response (XDR) contains everything you need to detect threats and stop cyber attacks.
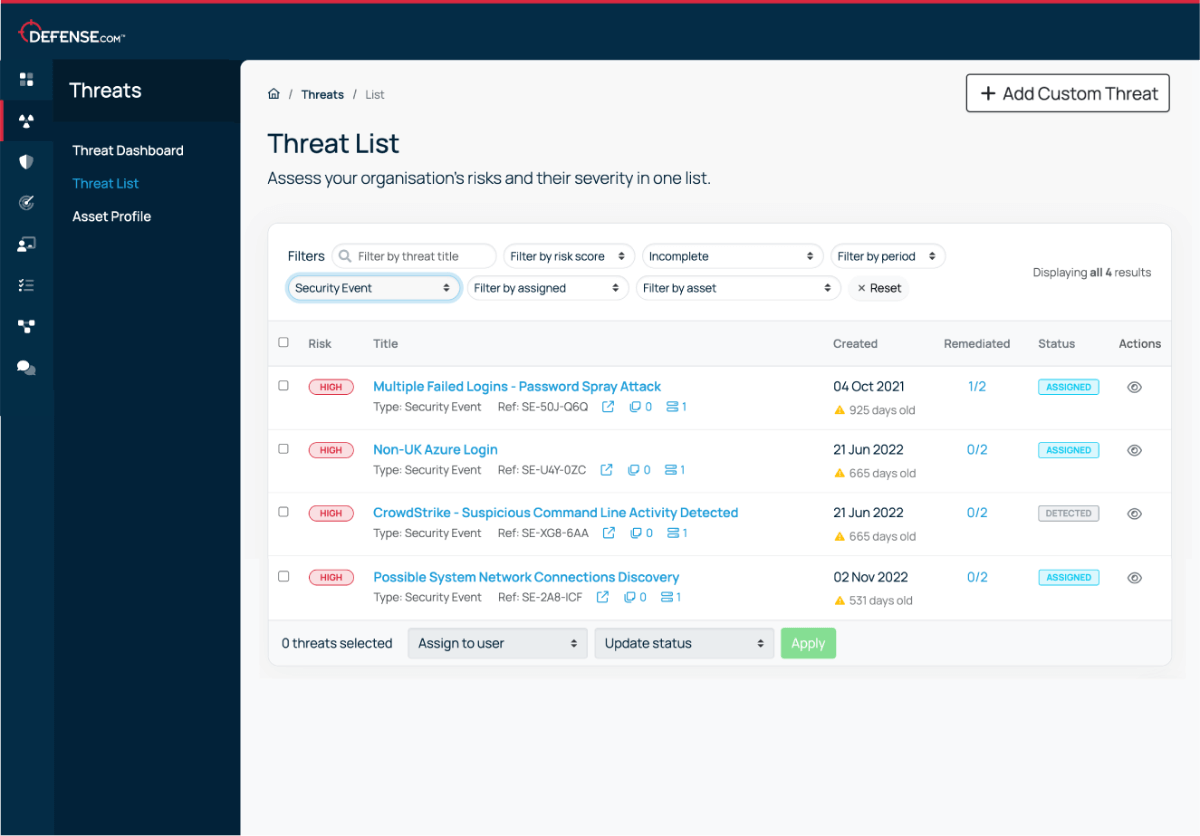
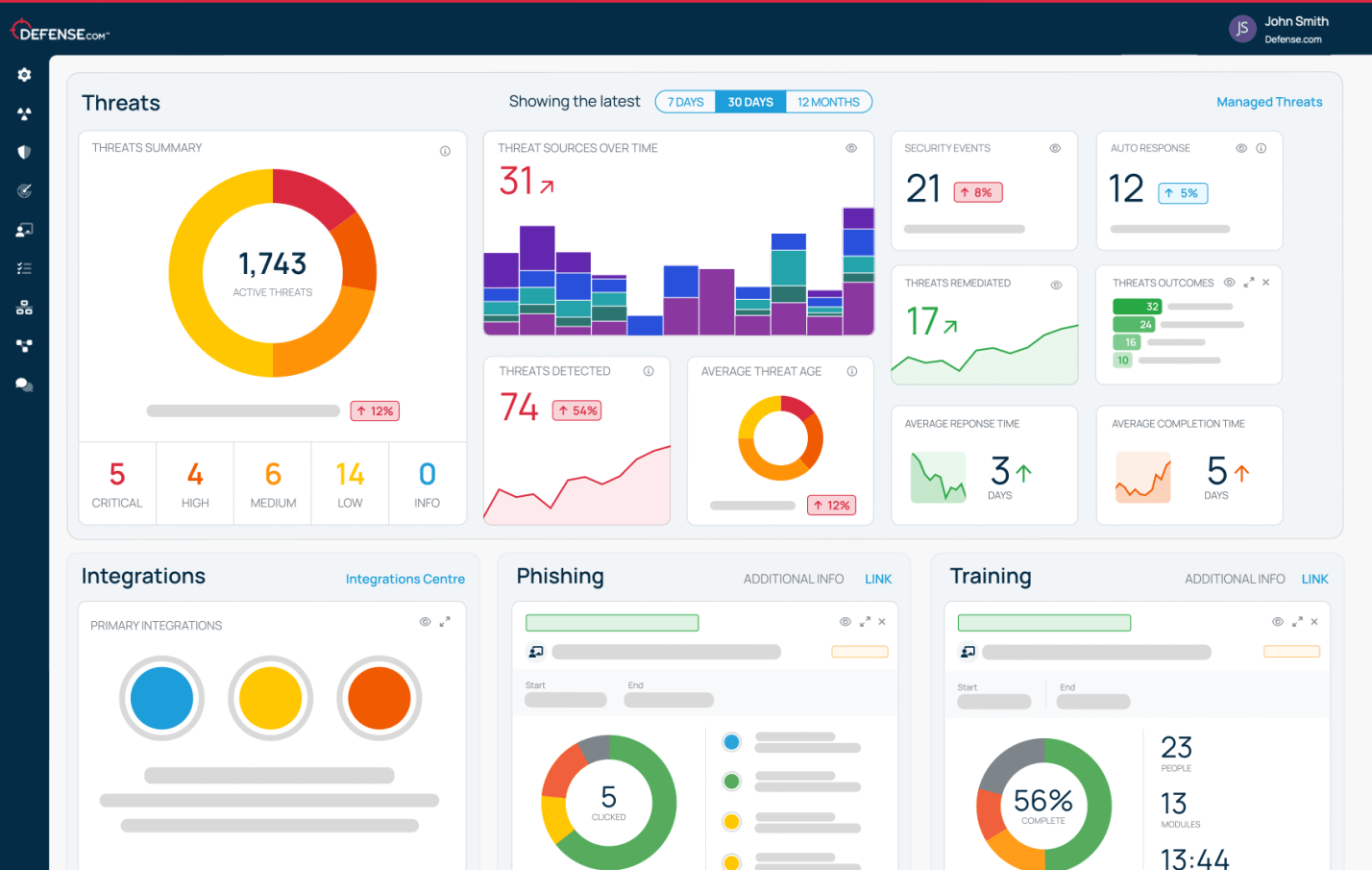
With Defense.com you can easily identify, prioritise and remediate threats from a single platform. Ingest and correlate security data from any source to simplify your security operations and reduce cyber risk.
Try for free

























Make threat management easier by combining telemetry from your whole security stack in one place.
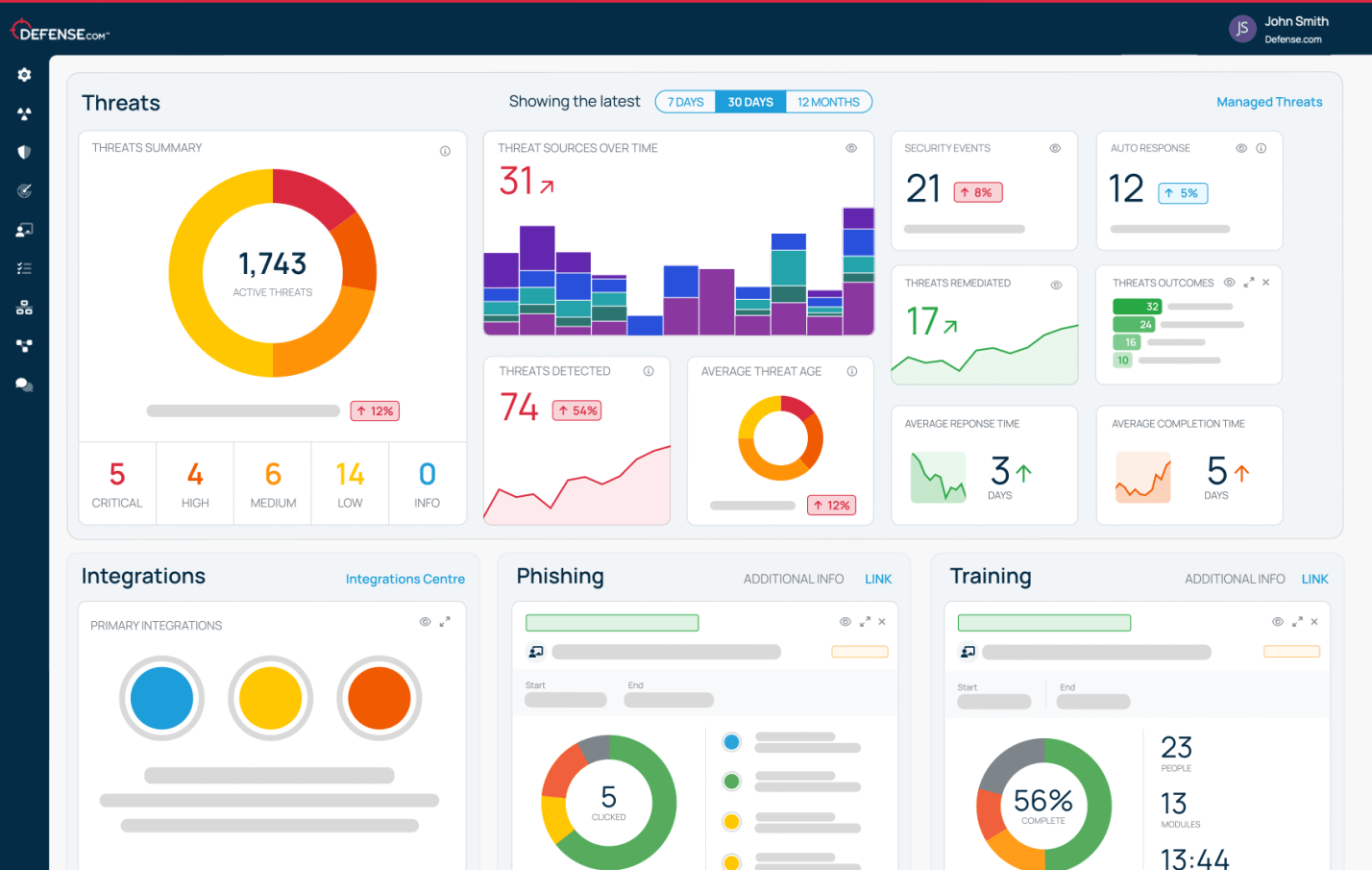
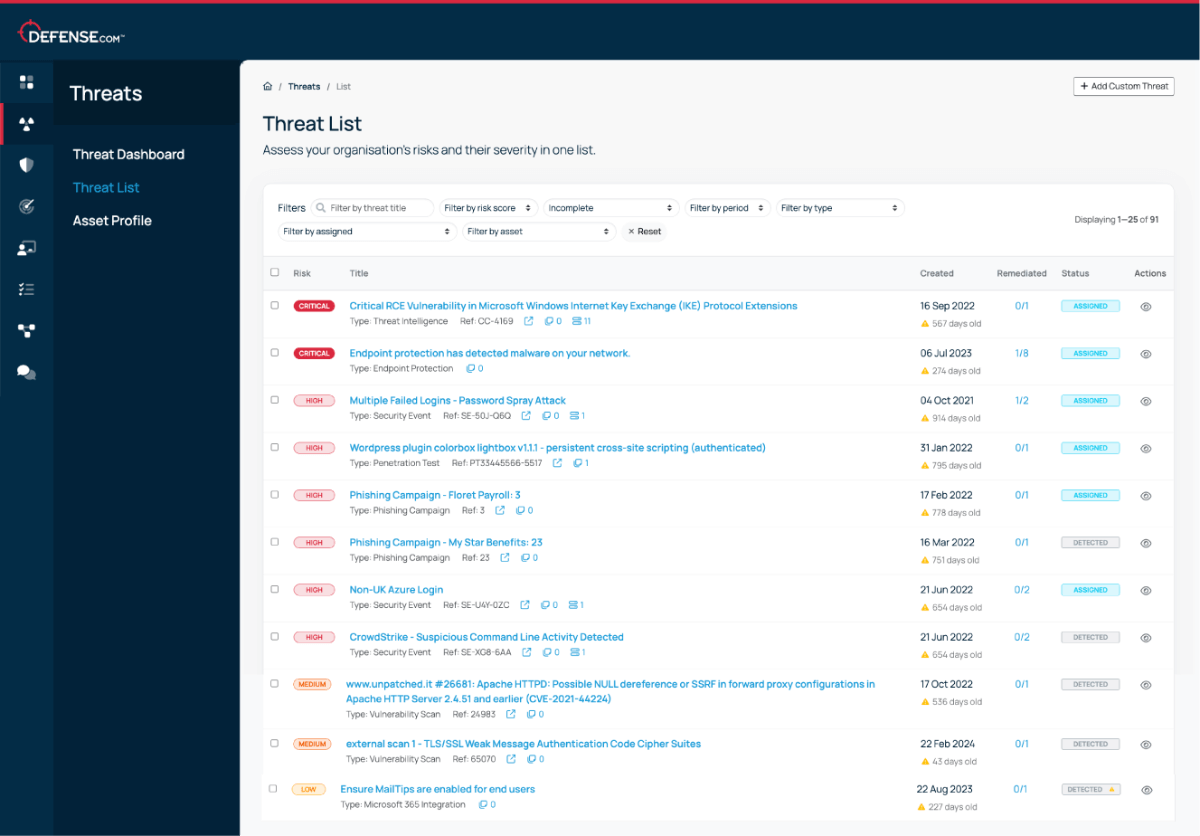
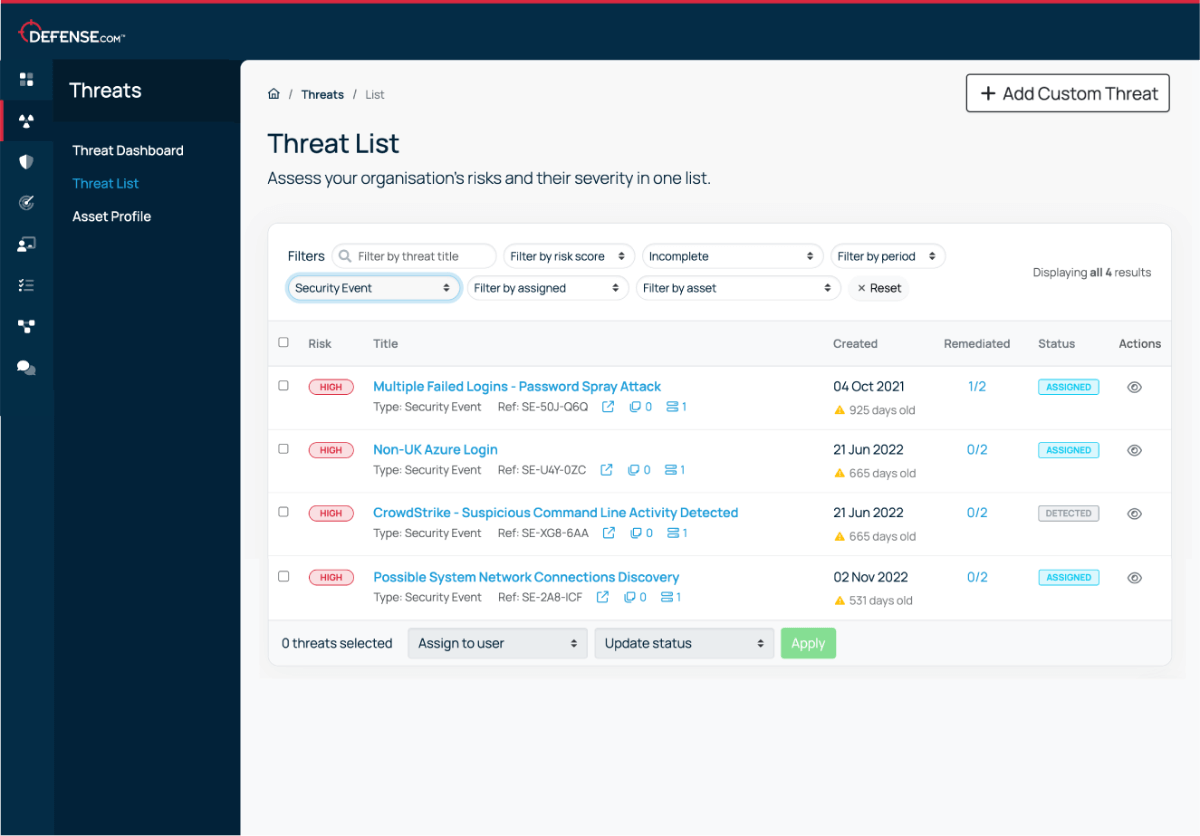
Get alerted to new threats and vulnerabilities affecting all areas of your business, all in one place. Each alert is prioritised based on criticality, so you can focus on the most important issues first.
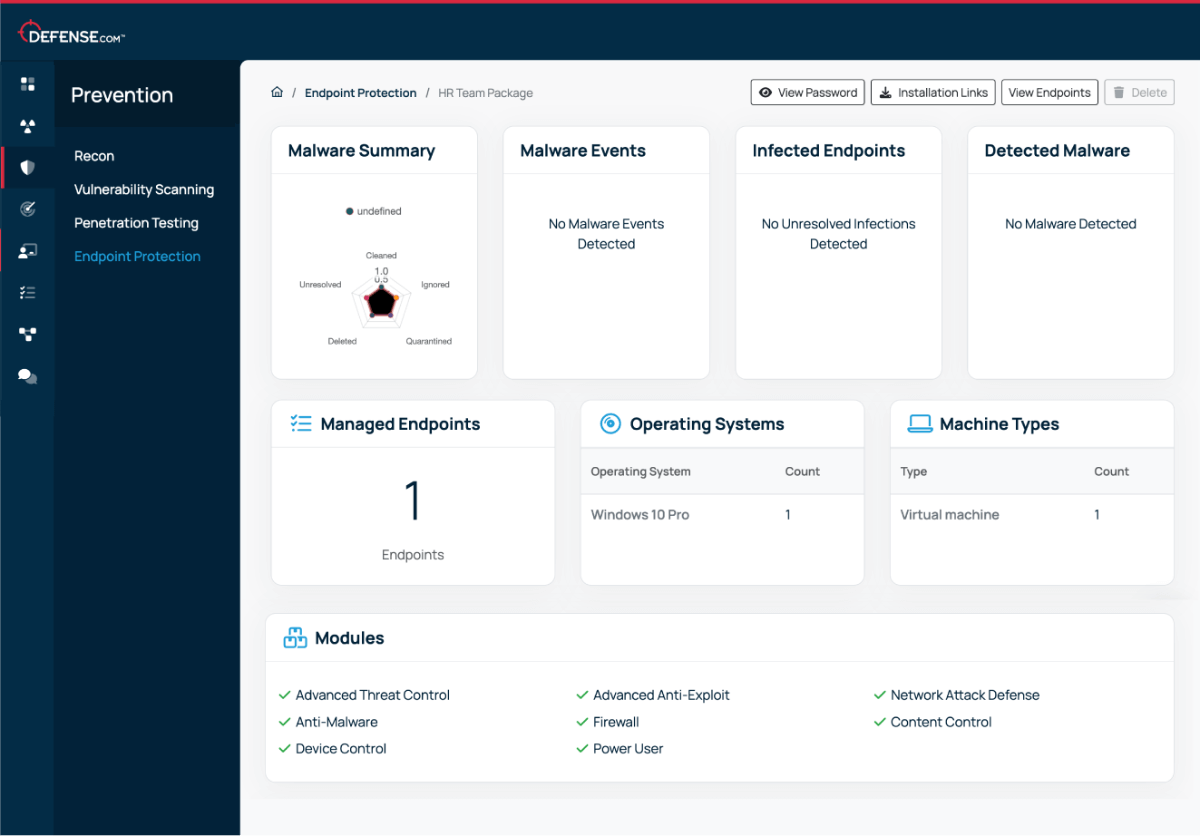
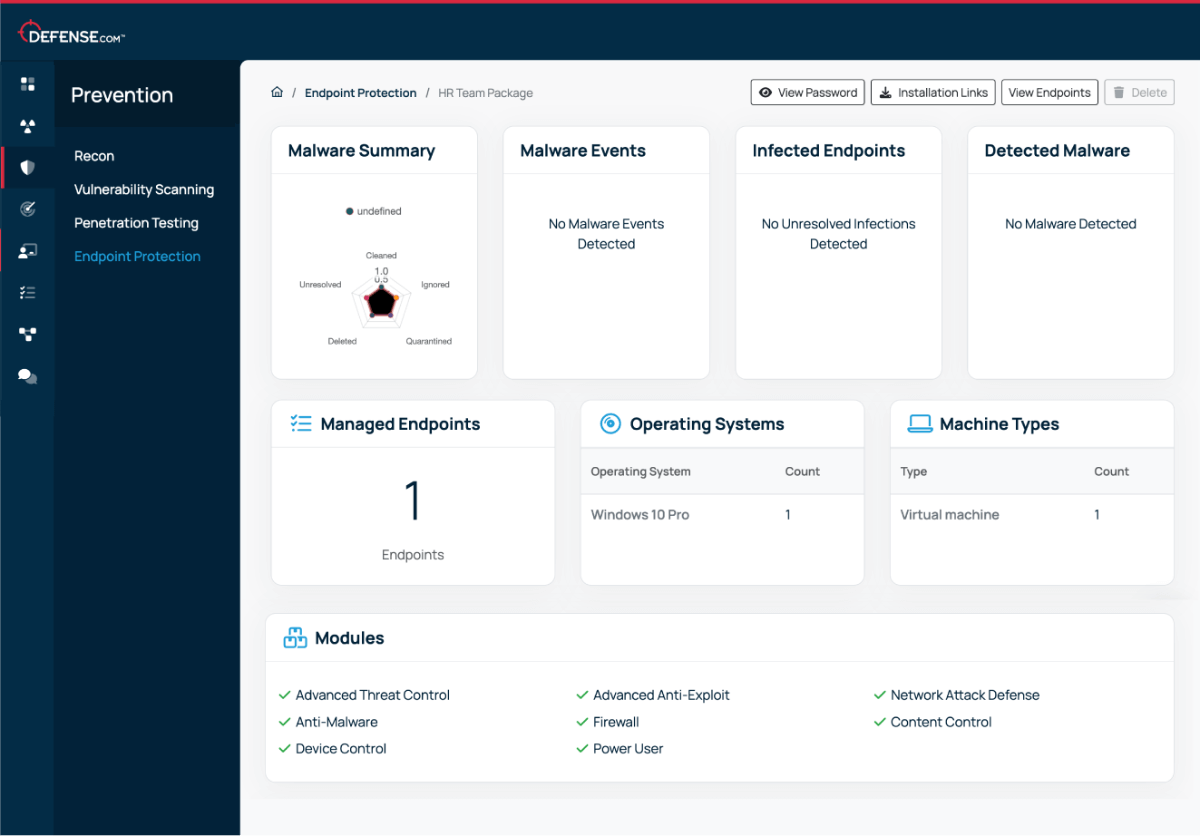
Protect your business and assets with automatic blocking of malware, fileless attacks, advanced exploits, ransomware, network attacks and much more.
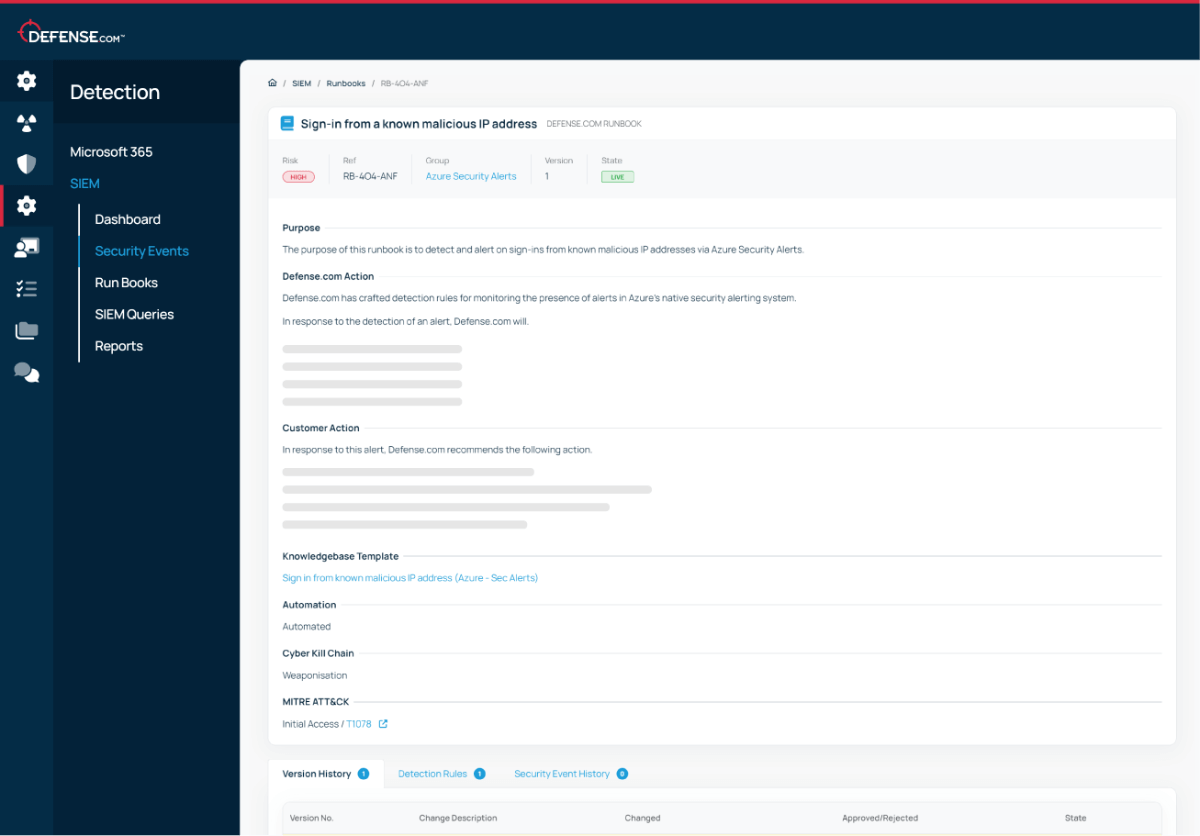
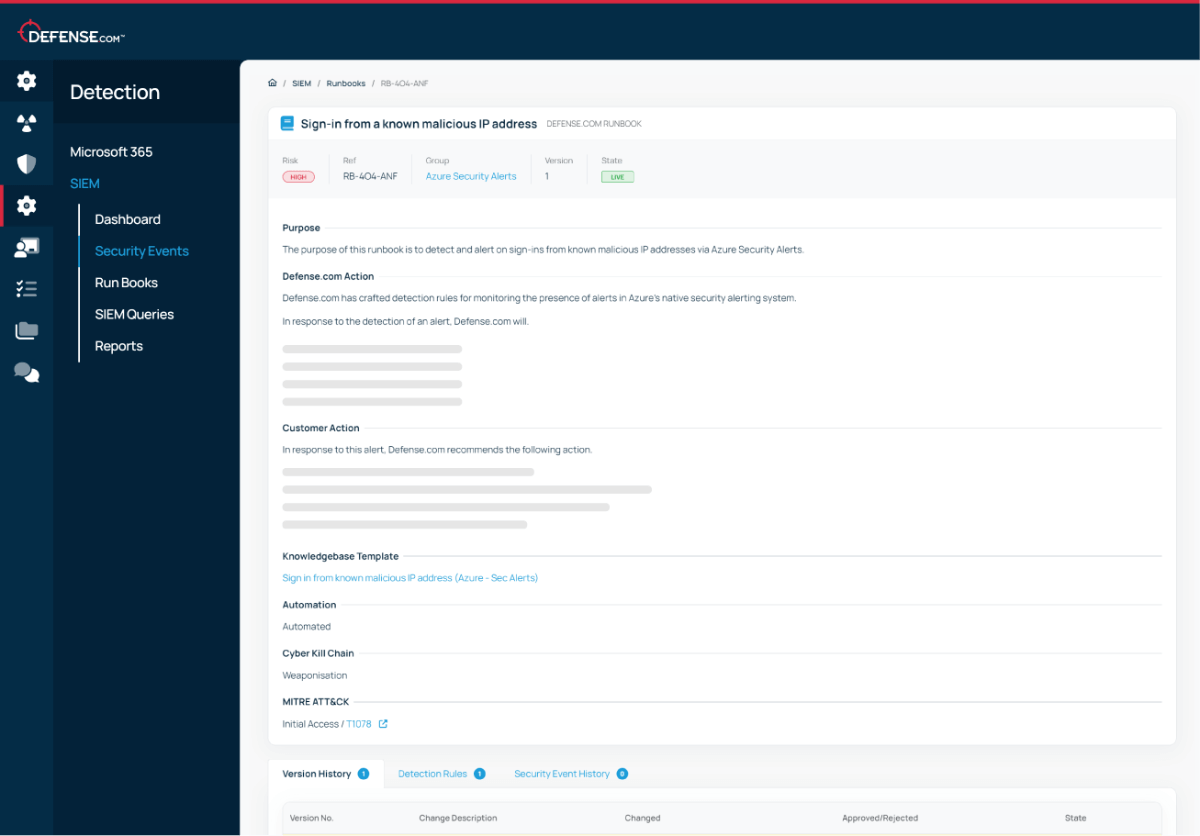
Quickly stop attacks and limit lateral movement with endpoint isolation. Detailed runbooks and step-by-step remediation advice helps you respond to threats faster and stop breaches.
We believe that good cyber security doesn’t have to be complicated. That’s why Defense.com provides you with the detection and response capabilities to effectively reduce your cyber risk.
By combining security tools that identify threats across your environment, Defense.com enables you to prioritise and manage cyber threats with ease. Remediation advice provided by experienced security analysts ensures threats are dealt with quickly and efficiently.

Defense.com XDR collects security telemetry from a range of sources, including:
No! Many XDR solutions on the market only work with native tools, leaving you locked in to one vendor. Defense.com does things differently and lets you collect data from any third party source, which means you don’t have to rip and replace your existing security technologies or stay tied to a single vendor.
Defense.com does offer a native endpoint protection agent to help you free up your budget without compromising on security, but this is not mandatory.
Defense.com XDR is easy to use on its own, but if you’d prefer to outsource your security operations, we can help.
Our managed security services take the pressure off your internal team and help you prevent breaches. Expert SOC analysts will monitor your environment 24/7 and raise threats to your attention, so you can focus on other tasks. Find out more about Managed SIEM.